Virtual Networks : 7 Powerful Insights You Must Know
Virtual Networks (VNet) are no longer just a buzzword—they’re the backbone of modern cloud infrastructure. Whether you’re scaling a startup or managing enterprise systems, understanding VNets can transform how you handle security, connectivity, and scalability in the cloud.
What Are Virtual Networks (VNet)?

At its core, a Virtual Network (VNet) is a representation of your own network in the cloud. It allows you to launch cloud resources in a logically isolated virtual space that you define. Think of it as building your private digital neighborhood within a massive public cloud environment like Microsoft Azure, Amazon Web Services (AWS), or Google Cloud Platform (GCP).
Virtual Networks (VNet) enable you to control IP address ranges, subnets, routing tables, and network gateways. They act as the foundation for secure communication between virtual machines (VMs), applications, and on-premises networks. Without a properly configured VNet, cloud resources would be exposed and disorganized—like cars on a highway without lanes or traffic rules.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Core Components of a VNet
Every Virtual Network (VNet) is built from several essential components that work together to ensure seamless and secure connectivity. These include:
- Subnets: Segments within a VNet that divide the network into smaller, manageable parts for better organization and security.
- IP Address Ranges: Defined using CIDR notation (e.g., 10.0.0.0/16), these determine how many devices can connect and how traffic is routed.
- Network Security Groups (NSGs): Act as virtual firewalls controlling inbound and outbound traffic to resources.
- Route Tables: Define how packets are directed between subnets and external destinations.
Understanding these components is crucial when designing scalable and secure cloud architectures. For example, Azure’s documentation on Virtual Network Overview provides an in-depth look at how these elements interact.
How Virtual Networks (VNet) Work in the Cloud
When you create a Virtual Network (VNet), you’re essentially defining a boundary for your cloud resources. Within this boundary, VMs, containers, and other services can communicate securely. The VNet uses software-defined networking (SDN) to abstract physical hardware, allowing dynamic configuration and automation.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Data travels through the VNet via encapsulated packets, often using protocols like VXLAN or NVGRE. This encapsulation ensures isolation even though multiple VNets may coexist on the same physical infrastructure. Cloud providers use overlay networks to maintain performance and security across shared environments.
For instance, in AWS, a VPC (Virtual Private Cloud) serves the same purpose as a VNet in Azure. You can explore AWS’s approach at AWS Virtual Private Cloud, which offers similar capabilities with slight differences in terminology and implementation.
“A well-designed Virtual Network (VNet) is the foundation of cloud security and performance.” — Cloud Architecture Best Practices, Microsoft Azure
Key Benefits of Using Virtual Networks (VNet)
Deploying Virtual Networks (VNet) isn’t just about replicating on-premises networks in the cloud—it’s about unlocking new levels of flexibility, control, and efficiency. Organizations that leverage VNets effectively see measurable improvements in security, scalability, and operational agility.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Let’s explore the most impactful advantages of implementing Virtual Networks (VNet) in your cloud strategy.
Enhanced Security and Isolation
One of the biggest strengths of Virtual Networks (VNet) is the ability to isolate workloads. By segmenting your environment into subnets, you can apply granular security policies. For example, a web server subnet can allow public internet access, while a database subnet remains completely private.
You can further tighten security using:
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
- Network Security Groups (NSGs): Filter traffic based on IP, port, and protocol.
- Application Security Groups (ASGs): Group resources by role (e.g., ‘web tier’) and apply rules dynamically.
- Private Endpoints: Allow secure access to services like Azure Storage without exposing them to the public internet.
This layered defense model reduces the attack surface and helps meet compliance standards like GDPR, HIPAA, or PCI-DSS.
Scalability and Flexibility
Virtual Networks (VNet) are inherently scalable. You can start small with a single subnet and expand as your application grows. Need more IP addresses? Adjust your CIDR block. Launching a new microservice? Spin up a new subnet in minutes.
Cloud providers also support global peering and cross-region connectivity, enabling distributed applications to function as a unified system. For example, Azure allows VNet peering across regions, making it easy to deploy resilient, multi-region architectures.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
This flexibility is especially valuable for DevOps teams using Infrastructure as Code (IaC) tools like Terraform or ARM templates to automate VNet deployment.
Cost Efficiency and Resource Optimization
While cloud networking might seem abstract, it directly impacts your bottom line. Virtual Networks (VNet) help reduce costs by minimizing data transfer fees and optimizing resource placement.
For example:
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
- Traffic within the same VNet is usually free, while data crossing regions or going to the internet incurs charges.
- Using internal load balancers instead of public ones reduces exposure and cost.
- Private connectivity via ExpressRoute or Direct Connect avoids public internet egress fees.
By designing efficient VNets, organizations can save thousands annually on cloud bills. Detailed pricing models are available on Azure Virtual Network Pricing.
Virtual Networks (VNet) in Major Cloud Platforms
Different cloud providers offer their own implementations of Virtual Networks (VNet), each with unique features and integration capabilities. While the core concept remains consistent, understanding platform-specific nuances is key to maximizing performance and compatibility.
Let’s compare how Virtual Networks (VNet) are implemented across the top three cloud providers: Microsoft Azure, Amazon Web Services (AWS), and Google Cloud Platform (GCP).
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Microsoft Azure Virtual Network (VNet)
In Microsoft Azure, Virtual Networks (VNet) are central to networking architecture. Azure VNets support IPv4 and IPv6, custom DNS settings, and seamless integration with Azure Active Directory and hybrid environments.
Key features include:
- VNet Peering: Connect VNets within or across regions with low latency.
- Service Endpoints: Securely link Azure services (like SQL Database) to your VNet.
- Private Link: Access Azure PaaS services over a private IP address.
- Integration with On-Premises: Use Site-to-Site VPN or Azure ExpressRoute for hybrid connectivity.
Azure’s VNet also integrates tightly with Azure Firewall, Network Watcher, and DDoS Protection, making it ideal for enterprise-grade deployments. Learn more at Azure Virtual Network Documentation.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
AWS Virtual Private Cloud (VPC)
AWS calls its version of Virtual Networks (VNet) a Virtual Private Cloud (VPC). A VPC allows you to define a virtual network closely resembling a traditional data center network.
Notable capabilities include:
- Subnet Types: Public, private, and isolated subnets for different security zones.
- Internet Gateway: Enables internet access for public subnets.
- NAT Gateway: Allows private instances to reach the internet without being exposed.
- Security Groups and NACLs: Layered firewall controls at instance and subnet levels.
VPCs can span multiple Availability Zones for high availability and support VPC peering, Transit Gateway, and Direct Connect for complex network topologies. Explore AWS VPC at AWS VPC User Guide.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Google Cloud VPC
Google Cloud Platform (GCP) uses Virtual Private Cloud (VPC) as its implementation of Virtual Networks (VNet). GCP’s VPC stands out with its global scope—subnets can span multiple regions within the same VPC.
Unique features include:
- Global Subnets: One subnet can extend across regions, simplifying IP management.
- Firewall Rules by Tag: Apply security policies based on instance tags.
- Cloud NAT: Enables outbound internet access for private instances.
- Shared VPC: Centralized networking management for multiple projects.
GCP also integrates with Cloud Interconnect and Partner Interconnect for hybrid setups. More details at Google Cloud VPC Overview.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Designing a Secure and Scalable Virtual Network (VNet)
Building a Virtual Network (VNet) isn’t just about connecting resources—it’s about doing so securely, efficiently, and with future growth in mind. A poorly designed VNet can lead to security gaps, performance bottlenecks, and management nightmares.
Follow these best practices to ensure your Virtual Networks (VNet) are robust and future-proof.
Planning IP Addressing and Subnetting
Before creating a VNet, plan your IP addressing scheme carefully. Choose a CIDR block that provides enough addresses for current and future needs, but avoid overly large ranges that waste IP space.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Common practices include:
- Use 10.0.0.0/8, 172.16.0.0/12, or 192.168.0.0/16 for private networks.
- Divide your VNet into subnets like 10.0.1.0/24 for web tier, 10.0.2.0/24 for app tier, and 10.0.3.0/24 for database tier.
- Reserve space for future expansion and hybrid connectivity.
Tools like IP Address Management (IPAM) systems can help track allocations and prevent conflicts, especially in large organizations.
Implementing Network Security Groups (NSGs)
Network Security Groups (NSGs) are critical for enforcing security policies in Virtual Networks (VNet). They function like firewalls, allowing or denying traffic based on source, destination, port, and protocol.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Best practices for NSG configuration:
- Apply NSGs at both subnet and individual resource levels for defense in depth.
- Use descriptive rule names (e.g., ‘Allow-HTTP-From-Web’) for easier auditing.
- Deny all inbound traffic by default and only allow what’s necessary.
- Regularly review and clean up unused rules to reduce complexity.
In Azure, NSGs support service tags (e.g., ‘Internet’, ‘AzureLoadBalancer’) and application security groups, making rule management more dynamic.
Using Route Tables and Custom Routing
Custom route tables allow you to control how traffic flows within and beyond your Virtual Networks (VNet). By default, cloud platforms provide system routes for local, internet, and peering traffic.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
You can override these with user-defined routes (UDRs) to:
- Route traffic through a virtual appliance (e.g., firewall or IDS/IPS).
- Force tunneling internet-bound traffic through on-premises for inspection.
- Direct traffic to specific gateways or endpoints.
For example, in a hub-and-spoke model, the hub VNet contains shared services and security appliances, while spoke VNets route traffic through it using UDRs.
“Design your VNet like a city: plan roads (routes), zones (subnets), and checkpoints (firewalls) before construction begins.”
Connecting Virtual Networks (VNet) Across Environments
Modern applications rarely exist in isolation. They often span multiple VNets, cloud regions, or even on-premises data centers. Connecting these environments securely and efficiently is a key challenge that Virtual Networks (VNet) are designed to solve.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Let’s explore the primary methods for interconnecting VNets and hybrid networks.
VNet Peering: Direct Internal Connectivity
VNet peering allows two VNets to communicate as if they were on the same network. Traffic flows through the cloud provider’s backbone, not the public internet, ensuring high performance and security.
Key characteristics:
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
- Low latency and high bandwidth.
- No need for gateways or public IPs.
- Supports both regional and global peering (in Azure and AWS).
- Non-transitive: If VNet A peers with B, and B with C, A cannot talk to C unless explicitly peered.
VNet peering is ideal for microservices architectures, shared services hubs, or disaster recovery setups. Learn more about Azure VNet peering at Azure VNet Peering Overview.
Site-to-Site VPN: Secure Hybrid Connections
For organizations with on-premises data centers, Site-to-Site VPN provides encrypted connectivity between local networks and Virtual Networks (VNet) in the cloud.
How it works:
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
- A VPN gateway is deployed in the VNet.
- An on-premises VPN device (e.g., Cisco, Juniper) establishes an IPsec/IKE tunnel.
- Traffic between sites is encrypted and routed securely.
This method is cost-effective and widely supported, though it depends on internet bandwidth and may introduce latency. It’s perfect for backup, migration, or gradual cloud adoption.
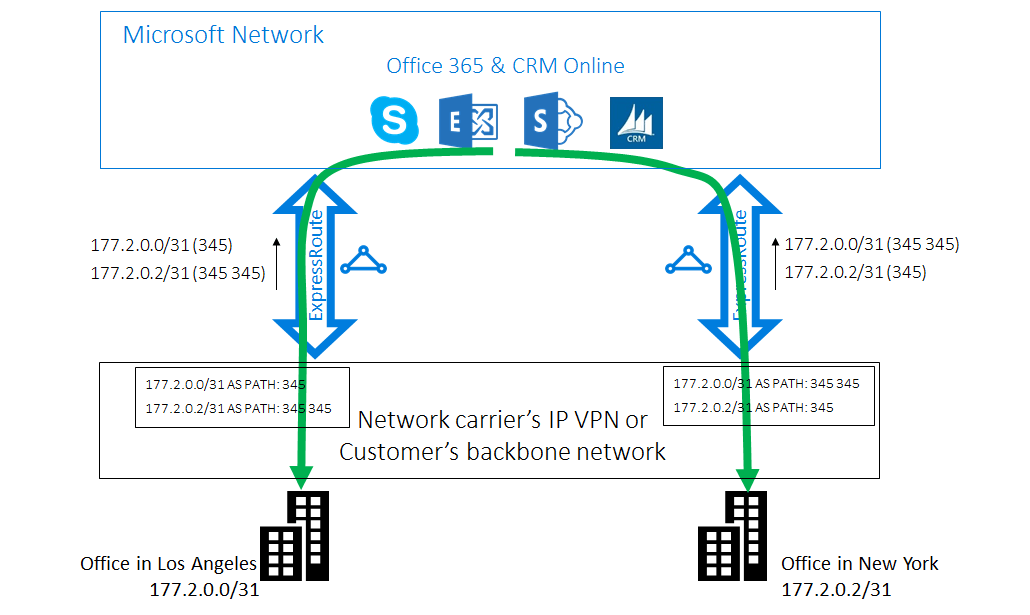
Azure ExpressRoute and AWS Direct Connect
For mission-critical applications requiring higher reliability and performance, dedicated private connections like Azure ExpressRoute or AWS Direct Connect are the gold standard.
Benefits include:
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
- Private connectivity via a colocation provider or network partner.
- No public internet exposure.
- Higher bandwidth (up to 100 Gbps).
- Lower latency and jitter.
- Service Level Agreements (SLAs) for uptime.
These solutions are more expensive but essential for regulated industries or high-performance computing. Details available at Azure ExpressRoute and AWS Direct Connect.
Advanced Features of Virtual Networks (VNet)
Beyond basic connectivity, Virtual Networks (VNet) offer advanced capabilities that empower organizations to build intelligent, secure, and automated cloud networks.
These features go beyond traditional networking, leveraging cloud-native innovations to solve complex challenges.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Private Endpoints and Service Endpoints
Service Endpoints and Private Endpoints allow secure access to cloud platform services (like databases or storage) without exposing them to the public internet.
Differences:
- Service Endpoints: Securely extend your VNet to Azure services using private IPs within your address space.
- Private Endpoints: Use Azure Private Link to assign a private IP from your VNet directly to the service, making it appear as if it’s hosted inside your network.
Private Endpoints provide the highest level of isolation and are recommended for sensitive workloads. Learn more at Azure Private Link.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Network Watcher and Monitoring Tools
Monitoring is critical for maintaining performance and security in Virtual Networks (VNet). Azure Network Watcher, AWS VPC Flow Logs, and GCP Packet Mirroring provide deep visibility into network traffic.
Key monitoring capabilities:
- Flow logs to capture allowed and denied traffic.
- Connection troubleshooters to diagnose reachability issues.
- IP flow verify to check if traffic is blocked by NSGs.
- Topology maps to visualize network layout.
These tools help detect anomalies, troubleshoot connectivity, and meet compliance requirements.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Integration with Cloud Firewalls and Security Appliances
While built-in security groups are powerful, complex environments often require next-generation firewalls (NGFWs) for advanced threat protection.
You can deploy virtual appliances like:
- Azure Firewall (managed)
- Palo Alto VM-Series
- Cisco Firepower
- Check Point CloudGuard
These appliances can be placed in a dedicated subnet (DMZ) and integrated with route tables to inspect all inbound and outbound traffic, providing IDS/IPS, URL filtering, and decryption capabilities.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Common Challenges and How to Avoid Them
Despite their benefits, Virtual Networks (VNet) can introduce complexity if not managed properly. Many organizations face recurring issues that impact performance, security, and scalability.
Here are the most common pitfalls and how to avoid them.
IP Address Conflicts in Hybrid Setups
When connecting on-premises networks to the cloud, overlapping IP ranges can cause routing issues and connectivity failures.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Solution:
- Conduct a full audit of on-premises IP usage before designing your VNet.
- Avoid using common ranges like 192.168.0.0/24 if they’re already in use locally.
- Use tools like Azure Migrate to assess and plan IP space.
Proper planning prevents costly re-IP projects later.
Overly Permissive Security Rules
It’s tempting to open broad ports (e.g., 0.0.0.0/0 on port 22) for convenience, but this creates major security risks.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Best practices:
- Follow the principle of least privilege.
- Use NSGs to restrict SSH/RDP access to specific IPs or jump boxes.
- Implement Just-In-Time (JIT) access for temporary administrative access.
Regular audits and automated compliance checks can catch misconfigurations early.
Complexity in Multi-VNet Architectures
As organizations grow, they often end up with dozens of VNets, leading to management overhead and inconsistent policies.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Mitigation strategies:
- Adopt a hub-and-spoke model with centralized governance.
- Use Infrastructure as Code (IaC) to enforce standards.
- Leverage Azure Policy or AWS Config to automate compliance.
Centralized management reduces drift and improves security posture.
What is a Virtual Network (VNet)?
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
A Virtual Network (VNet) is a logically isolated network in the cloud that enables secure communication between cloud resources, on-premises networks, and the internet. It provides control over IP addressing, subnets, routing, and security policies.
How does VNet peering work?
VNet peering connects two virtual networks, allowing resources to communicate using private IP addresses. Traffic flows over the cloud provider’s backbone network, ensuring low latency and high security without going through the public internet.
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
Can I connect my on-premises network to a VNet?
Yes, you can connect your on-premises network to a Virtual Network (VNet) using Site-to-Site VPN or dedicated connections like Azure ExpressRoute or AWS Direct Connect for secure, high-performance hybrid networking.
Are there costs associated with using Virtual Networks (VNet)?
Virtual Networks (VNet) – Virtual Networks (VNet) menjadi aspek penting yang dibahas di sini.
While creating a VNet is typically free, costs arise from data transfer, gateways (VPN/ExpressRoute), public IP addresses, and bandwidth usage. Inbound data is usually free, but outbound egress traffic incurs charges based on volume and destination.
What is the difference between Service Endpoints and Private Endpoints?
Service Endpoints secure access to Azure services over the Microsoft backbone network using VNet identity. Private Endpoints go further by assigning a private IP from your VNet to the service, making it appear as part of your internal network and providing full private connectivity.
Virtual Networks (VNet) are the cornerstone of modern cloud infrastructure, offering unparalleled control over connectivity, security, and scalability. From basic subnet design to advanced hybrid connectivity and private access, mastering VNets empowers organizations to build resilient, efficient, and secure cloud environments. Whether you’re on Azure, AWS, or GCP, the principles remain consistent: plan carefully, secure by default, and automate for scale. As cloud adoption accelerates, a deep understanding of Virtual Networks (VNet) will remain a critical skill for IT professionals and architects alike.
Recommended for you 👇
Further Reading: